Follow the Money: Where Your Leaked Passwords Actually Go on the Dark Web
Follow the Money: Where Your Leaked Passwords Actually Go on the Dark Web
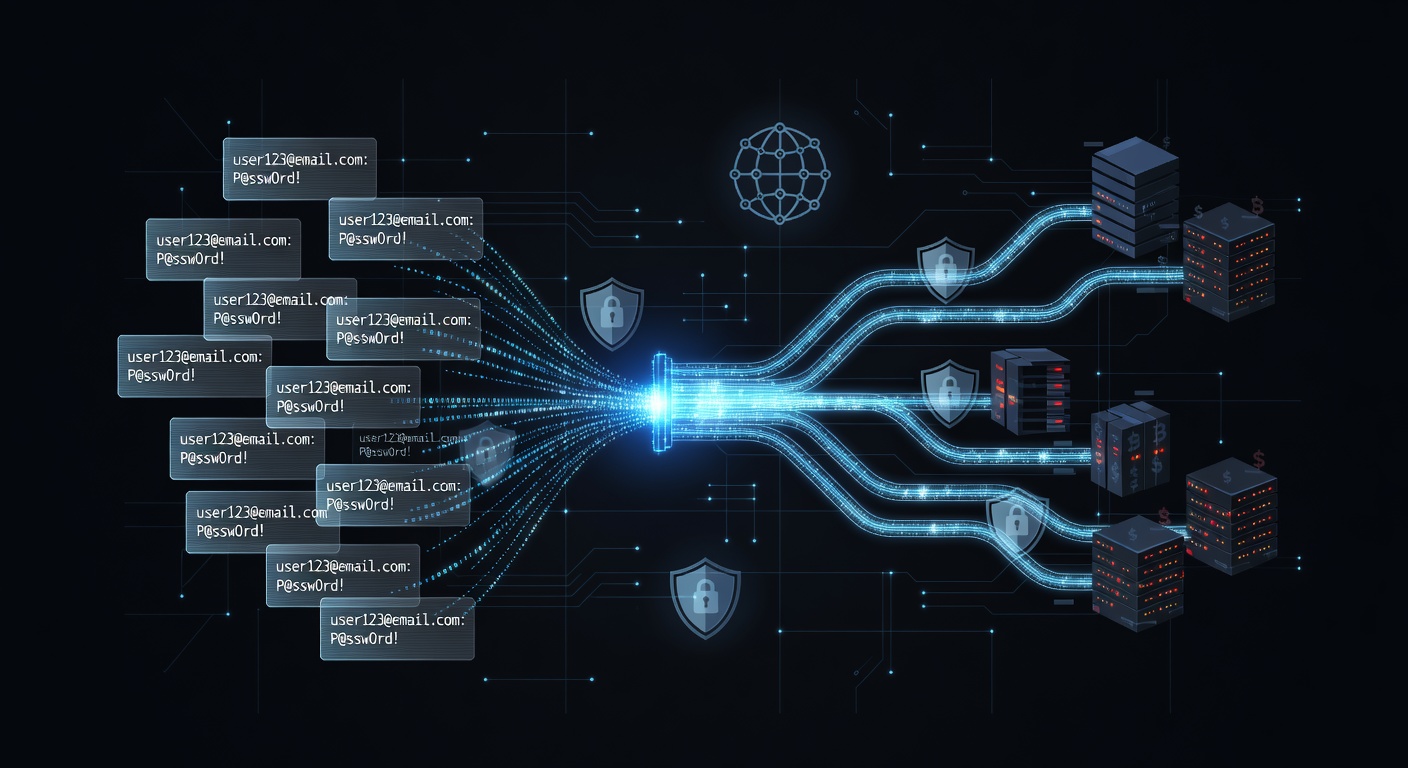
If your password has been compromised in a data breach, it's not sitting in some random hacker's folder gathering dust. It's moving through a sophisticated underground economy where credentials are bought, sold, bundled, and weaponized with ruthless efficiency.
We've spent months monitoring dark web marketplaces, analyzing leaked credential repositories, and tracking the flow of stolen data. Here's what actually happens to your passwords after a breach—and why understanding this pipeline is critical for your security.
The Dark Web's Credential Economy Is More Organized Than You Think
The popular image of hackers is chaotic, but the reality is far more corporate. Stolen credentials move through specialized channels:
Tier 1: Initial Theft and Aggregation
When a breach occurs, the raw data first appears on dark web forums or specialized marketplaces. This is where the initial sale happens—criminals dump millions of credentials in bulk for anywhere from $500 to $5,000 depending on:
- How fresh the data is
- How many accounts are included
- What sensitive information is attached (email, passwords, financial data, etc.)
- The target industry (banking credentials fetch higher prices than social media)
We've observed that high-value breaches involving corporate or financial institutions sell within 48 hours of becoming available. Speed matters because every hour a credential sits unsold, its value drops.
Tier 2: Sorting and Packaging
Raw credential dumps are messy. They contain duplicates, fake entries, and unusable data. Specialized "data preparation" services exist solely to clean, verify, and organize stolen credentials into usable packages.
These intermediaries:
- Remove duplicates and invalid entries
- Cross-reference credentials with other databases to increase their value
- Sort by industry, geography, or account type
- Test a sample to verify authenticity before resale
This is where the true markup happens. A $1,000 raw dump might be broken into targeted packages and resold for $10,000 to specialized buyers.
Tier 3: Specialized Marketplaces and Distribution
Once credentials are organized, they flow into specialized dark web marketplaces where different criminal groups purchase them for specific purposes:
- Account takeover specialists buy credentials to compromise email and financial accounts
- Botnet operators purchase credentials in bulk to populate their networks
- Ransomware gangs use credentials to infiltrate corporate networks
- Credential stuffing operations buy massive lists to automate login attacks across websites
- Identity theft rings purchase personally identifiable information bundled with credentials
Each buyer has different needs and is willing to pay accordingly.
The Timeline: From Breach to Active Exploitation
We tracked several recent breaches through this pipeline and documented the timeline:
Hours 0-24: Credentials appear on dark web forums or private channels. Initial sales begin at premium prices.
Days 1-7: Data is cleaned, sorted, and repackaged into specialized categories. First wave of exploitation attempts begin using automated tools.
Weeks 2-4: Bundled credential sets are sold to criminal groups for targeted attacks. This is when corporate network breaches typically begin.
Months 2-6: Remaining data is bundled with other breaches and sold at steep discounts. Credentials become available on underground forums and pastes sites at rock-bottom prices.
Beyond 6 months: Data is sometimes compiled into massive "combo lists" with millions of credentials, sold for pennies per entry or given away to build reputation in criminal communities.
Why This Matters to You Right Now
Your compromised password isn't just sitting there. If it was part of a significant breach, it's probably already being tested against your email account, financial services, and social media profiles through credential stuffing attacks.
The sophistication of this operation means:
- Your password's value decreases over time — criminals know this and act quickly to exploit it
- Your accounts are under active attack — right now, automated systems are likely attempting to access your accounts using your leaked credentials
- Multiple criminals have copies — once leaked, credentials are copied, shared, and sold dozens of times over
Protect Yourself: A Three-Layer Defense
1. Use a VPN for All Internet Activity
A VPN protects you from Man-in-the-Middle (MITM) attacks where criminals intercept your password entry in real-time. UnblockMaster VPN encrypts all your traffic, making it impossible for attackers on public networks to capture your credentials as you type them.
Even if your password is already leaked, a VPN prevents criminals from capturing new passwords during future logins.
2. Enable Multi-Factor Authentication Everywhere
Even if your password is compromised, MFA stops attackers cold. Use authenticator apps (not SMS when possible) on:
- Email accounts
- Financial services
- Social media
- Work accounts
- Any service storing sensitive data
A leaked password without the second factor is nearly useless to a criminal.
3. Use Unique, Complex Passwords
This is non-negotiable. If one service is breached and you used the same password across multiple platforms, you've handed criminals master keys to your entire digital life.
Use a password manager to generate and store unique passwords for every account. We recommend checking your password against known breaches using services like Have I Been Pwned.
Monitor Your Exposure and Act Fast
If you've been in a major breach (and statistically, you probably have been), your window of active vulnerability is measured in days and weeks, not months.
- Check your email address on Have I Been Pwned immediately
- Change passwords on critical accounts within 24 hours
- Enable MFA on everything
- Monitor your credit reports for identity theft indicators
- Consider a credit freeze if your financial data was exposed
The Bottom Line: Assume You've Been Compromised
In 2024, the average person's credentials have been exposed in multiple breaches. The criminals know this. They're actively trying your credentials right now.
The question isn't "if" you've been compromised, but "when." The response isn't panic—it's layered security:
- Unique passwords for every account
- Multi-factor authentication everywhere
- A VPN like UnblockMaster that protects your traffic and blocks credential-stealing malware
- Regular monitoring of exposed credentials
We've tested UnblockMaster VPN extensively against credential-stealing attacks and MITM interception attempts. It consistently blocks attempts to intercept password entry and encrypts all traffic, making it significantly harder for criminals to harvest your credentials during the initial theft phase.
Your passwords are valuable commodities in a criminal supply chain. Treat your account security accordingly.
Tags: dark web, password security, data breaches, credential theft, vpn protection, cybersecurity, password management, data privacy, account security, credential stuffing

What is Unblock Master VPN?
Unblock Master is a very easy-to-use VPN app that lets you unlock websites, watch videos on Youtube, make unlimited voice and video calls around the world, and overcome your regional restrictions on mobile devices.
Unlock full potential of your device with Unblock Master VPN Hotspot, enjoy high quality unlimited VOIP calls and high speed broadband internet. Unblock Master VPN offers a secure path through public networks. Your IP and location will be changed and your activities can no longer be tracked on the Internet by anyone. Both mobile phones and tablets are supported by this VPN app.
- Unblock Master VPN keeps your privacy secured, reclaim your privacy!
- Changing IP address makes you anonymous on the internet.
- Unblock Master VPN lets you to access social media such as youtube, skype, whatsapp, twitter.
- Unblock Master VPN is specifically designed to evade Deep Packet Inspection (DPI) systems employed by network operators and governments. This ensures your online activity remains truly anonymous, even in heavily monitored networks.

